
Vectra AI
Paid ✓ VerifiedVectra AI detects active cyberattacks in hybrid and cloud environments using behavioral AI to identify lateral movement and escalation before breach.
📋 About Vectra AI
Vectra AI is a vectra ai network detection and response platform that uses AI to identify active cyberattacks moving laterally through hybrid and cloud environments. The platform focuses on behavioral detection — identifying the patterns that attackers exhibit while moving through a network after initial access — rather than relying solely on known malware signatures or rule-based alerts. This approach is designed to catch threats that bypass perimeter defenses and signature-based tools, which represent the majority of material breaches.
Vectra AI monitors network traffic, cloud infrastructure, identity systems, and endpoint behavior simultaneously to build a continuous picture of attacker movement. Alerts are prioritized by attack progression stage and affected entity urgency rather than generating undifferentiated noise that overwhelms security operations center analysts. The platform's Attack Signal Intelligence layer correlates events across sources to surface the highest-priority threats rather than leaving analysts to manually correlate hundreds of individual alerts.
Vectra AI targets enterprise security teams and managed security service providers who operate security operations centers and need to detect threats that have already bypassed preventive controls. The platform is deployed at organizations in finance, healthcare, critical infrastructure, and technology sectors where advanced persistent threat activity is a realistic operational concern rather than a theoretical risk.
⚡ Key Features of Vectra AI
Behavioral Threat Detection
Vectra AI analyzes network traffic, cloud API activity, and identity system behavior to identify attacker patterns rather than matching known malware signatures. Behavioral models are trained on attacker tactics, techniques, and procedures mapped to frameworks like MITRE ATT&CK. Detection fires on the behavior itself rather than requiring a known file hash or indicator of compromise. This approach surfaces threats that have bypassed signature-based preventive tools, which is the dominant pattern in serious incidents.
Attack Signal Intelligence
Correlates events across network, cloud, identity, and endpoint data sources to produce a consolidated attack narrative rather than a list of disconnected alerts. The prioritization layer scores entities by the urgency and progression stage of detected attack activity. Analysts receive a short list of the highest-priority entities requiring immediate investigation rather than hundreds of raw alerts to manually triage. This directly addresses alert fatigue, which is cited as a primary factor in missed detections in SOC environments.
Hybrid and Multi-Cloud Coverage
Monitors on-premises network infrastructure alongside AWS, Azure, and GCP cloud environments through a unified detection layer. Hybrid coverage closes the visibility gap that exists when detection tools are siloed by environment — attackers moving between on-premises and cloud assets are tracked continuously. A single platform interface covers all monitored environments without requiring separate tools per environment. This is increasingly critical as most enterprise environments span both on-premises and cloud infrastructure.
Identity Threat Detection
Monitors identity and access management systems including Active Directory and Azure AD for the privilege escalation and lateral movement patterns that attackers use after initial access. Identity-based attacks are the primary vector in enterprise breaches, and signature-based tools have limited visibility into identity system abuse. Vectra detects anomalous authentication patterns, Kerberoasting, and privilege escalation attempts as behavioral signals rather than known-bad indicators. Integration with identity infrastructure extends detection beyond network traffic alone.
SIEM and SOAR Integration
Integrates with major SIEM platforms and SOAR tools to feed prioritized threat signals into existing SOC workflows rather than requiring a separate investigation interface. Alert forwarding to Splunk, Microsoft Sentinel, and other platforms keeps Vectra data part of the analyst's existing toolchain. SOAR integration enables automated containment playbooks to execute on Vectra detections without manual SOC intervention. This embeds Vectra into established security operations processes.
Managed Detection Support
Supports managed security service provider deployments where the platform is operated on behalf of multiple client environments from a single multi-tenant management interface. MSSPs use Vectra to extend advanced detection capabilities to clients who lack in-house SOC resources. Multi-tenancy controls keep client environments isolated while enabling centralized management. This makes enterprise-grade behavioral detection accessible to organizations without fully staffed internal security teams.
🎯 Use Cases for Vectra AI
⚖️ Vectra AI Pros & Cons
Advantages
- ✓Behavioral detection catches threats that signature-based tools miss, including post-compromise lateral movement
- ✓Attack Signal Intelligence reduces alert volume and helps analysts focus on the highest-priority threats
- ✓Hybrid and multi-cloud coverage eliminates the visibility gaps that attackers exploit when moving between environments
- ✓Identity threat detection addresses the most common breach vector in enterprise environments
- ✓SIEM and SOAR integrations embed detection into existing SOC workflows without requiring a separate console
Drawbacks
- ✗Enterprise pricing and implementation complexity make the platform inaccessible to small and mid-size organizations without security teams
- ✗Behavioral models require a baseline period to establish normal patterns before detection accuracy reaches full effectiveness
- ✗False positive rates require analyst calibration in environments with unusual but legitimate network behaviors
- ✗Full value requires investment in integration with SIEM, identity, and endpoint platforms across the environment
📖 How to Use Vectra AI
Engage Vectra AI through vectra.ai to scope a deployment assessment for your environment.
Deploy Vectra sensors for network traffic capture and connect cloud and identity integrations for your monitored environments.
Allow the behavioral baseline period to complete so the platform establishes normal activity patterns for your environment.
Configure alert forwarding to your SIEM or SOAR platform to incorporate Vectra detections into existing SOC workflows.
Respond to prioritized entity alerts in the Attack Signal Intelligence dashboard, investigating the highest-scored entities first.
Review detection tuning and false positive feedback with Vectra's support team to calibrate models to your environment over time.
❓ Vectra AI FAQ
Vectra AI is a network detection and response platform that uses behavioral AI to identify active cyberattacks in hybrid and cloud environments. It focuses on detecting attacker behavior after initial access — lateral movement, privilege escalation, and data access — rather than relying on known malware signatures.
A SIEM collects and correlates log data from across the environment but requires analyst-written rules to detect threats. Vectra AI applies behavioral AI models to network and cloud traffic to detect attack patterns automatically without rule authoring. Vectra is typically integrated with a SIEM to feed prioritized, correlated detections into the existing SOC workflow.
Vectra AI monitors on-premises network traffic, AWS, Azure, and GCP cloud environments, and identity systems including Active Directory and Azure AD. Hybrid coverage tracks attacker movement across all of these environments from a single platform.
Vectra AI is an enterprise platform designed for organizations with security operations teams and complex hybrid environments. The pricing and implementation requirements are not suited to small businesses without dedicated security staff. Organizations without in-house SOC capabilities may access Vectra through managed security service providers.
Related to Vectra AI

Abnormal AI
Abnormal AI uses behavioral AI to detect business email compromise, account takeover, and socially engineered phishing that bypasses secure email gateways.

Norm AI
Norm AI is an enterprise compliance automation platform that translates regulatory requirements into machine-executable rules and monitors operational gaps in real time.
Featured on WhatIf.ai
Add this badge to your website to show you're listed on WhatIf AI
Alternatives to Vectra AI
A2E AI
A2E AI productivity platform converts audio and video recordings into transcripts, summaries, and action items with speaker identification.

Abnormal AI
Abnormal AI uses behavioral AI to detect business email compromise, account takeover, and socially engineered phishing that bypasses secure email gateways.
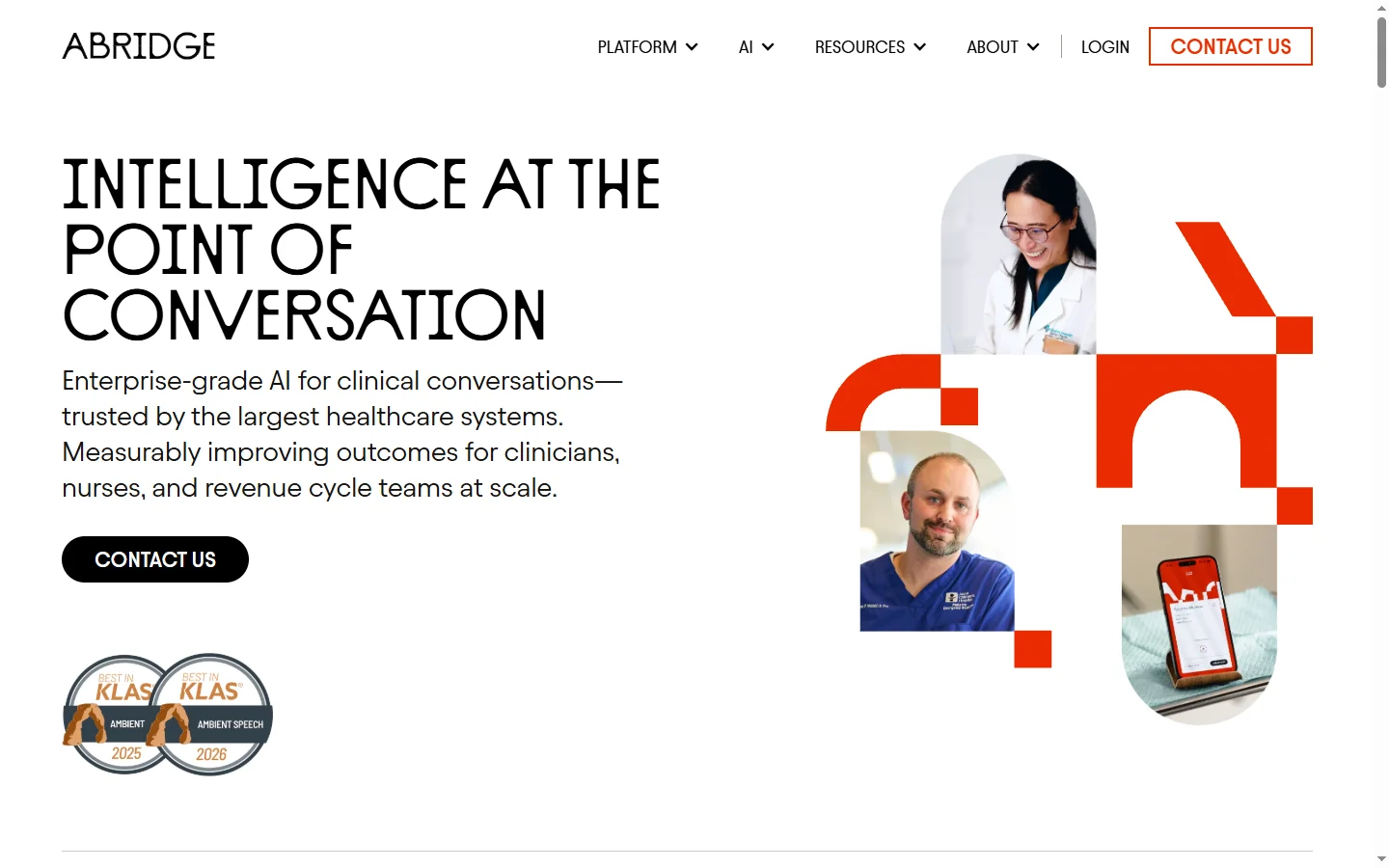

Abridge AI
Abridge AI medical documentation platform that records and summarizes clinical conversations into structured physician notes in real time.

Air AI
Air AI conducts autonomous full-length AI phone calls for sales prospecting, appointment setting, and customer service without human agents.